A newly discovered flaw in the Model Context Protocol (MCP) could put thousands of AI deployments at risk, exposing a critical vulnerability in AI infrastructure. This flaw allows any operating system command to be executed without proper sanitization, affecting major players like OpenAI and Google DeepMind who adopted MCP. Security teams need to act swiftly to protect their systems.
Anthropic developed MCP as an open standard for AI tools to communicate, and it’s become a cornerstone for AI agent-to-tool interactions. Despite its widespread adoption, a security flaw has been identified by OX Security researchers. The flaw lies in MCP’s STDIO transport, which executes any command it receives. This has led to more than 10 critical vulnerabilities across popular AI frameworks like LiteLLM and LangFlow. Anthropic, however, has declined to modify the protocol, arguing that input sanitization is the developer’s responsibility.
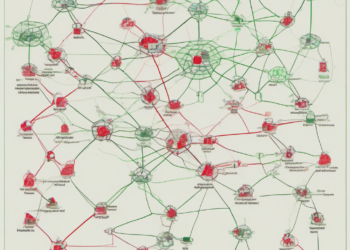
In the competitive landscape, MCP’s flaw raises questions about the reliability of open standards in AI. As Anthropic donated MCP to the Linux Foundation, its adoption skyrocketed, with downloads crossing 150 million. Yet, this flaw underscores a systemic issue: insecure defaults in protocol design. OX Security found 7,000 servers publicly exposed, estimating 200,000 vulnerable instances. This revelation could shake confidence in open standards and prompt a reevaluation of security practices.
For founders and engineers, this vulnerability highlights the importance of scrutinizing protocol defaults. The flaw isn’t just a technical oversight; it represents a broader challenge in managing AI infrastructure securely. Engineers must treat STDIO configurations as potential threat vectors, emphasizing sandboxing and rigorous input validation. Founders need to reassess their security strategies, ensuring their teams are prepared to handle such vulnerabilities.
Looking ahead, the real question is how the industry will respond to this vulnerability. Anthropic’s position remains unchanged, leaving developers to manage the risk. For tech leaders, this means prioritizing security audits and considering alternative protocols if necessary. The MCP flaw serves as a wake-up call, urging a shift from reactive patching to proactive security architecture. As the debate over responsibility continues, the immediate task is clear: protect your deployments and stay vigilant against potential exploits.