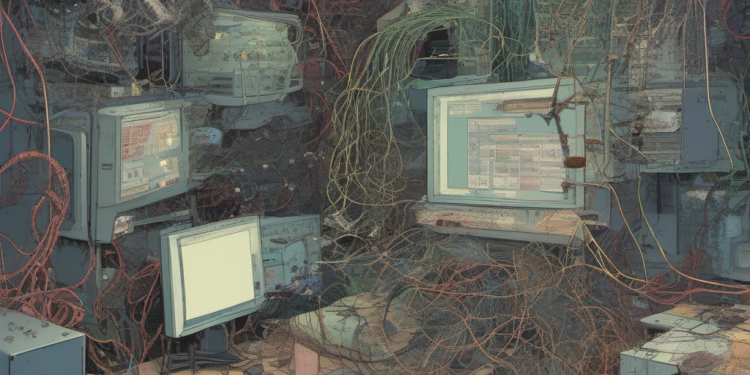
A new breed of digital vigilantes is emerging in the cybercrime landscape. An unidentified group of hackers has been infiltrating systems already compromised by the notorious cybercrime group TeamPCP. Their mission? To expel TeamPCP and scrub their nefarious tools from the networks. This unexpected twist in cyber warfare raises questions about digital ethics, cybersecurity practices, and the evolving tactics of those on the dark side of the internet.
## What This Hacker Group Is Doing
The mysterious group has set its sights on systems previously breached by TeamPCP, a cybercrime outfit known for its ransomware attacks and data exfiltration. Once inside these networks, the group undertakes a digital cleansing operation. They systematically remove backdoors and malware left behind by TeamPCP, effectively neutralizing the threat. While the intentions of this anonymous group remain unclear, their actions suggest a mission to disrupt the operations of established cybercriminals.
The methods employed by this group are sophisticated, suggesting a high level of technical expertise. They first gain access through vulnerabilities exploited by TeamPCP, then leverage their own tools to secure control. By ejecting TeamPCP from these systems, they are not only thwarting ongoing attacks but also potentially preventing future breaches by the same group.
## The Competitive Context: A New Frontier in Cybersecurity?
This development introduces a new dynamic in the cybersecurity arena, blurring the lines between hacker and protector. Traditional cybersecurity firms and law enforcement agencies have yet to comment on this phenomenon, which lies in a legal and ethical grey area. The concept of “hacking the hacker” challenges conventional strategies and raises questions about the legitimacy of such interventions.
TeamPCP is just one of many cybercrime groups operating globally, but their notoriety makes them a prime target for these vigilantes. The fact that another group can identify and neutralize their operations indicates a higher level of sophistication and possibly an insider’s perspective on cybercriminal operations. It also hints at a potential shift in cybercrime dynamics, where rival groups or individuals could start policing each other, either for ethical reasons or to gain a competitive edge.
## Implications for Founders, Engineers, and the Industry
For founders and engineers, this development underscores the complexity and unpredictability of the cybersecurity landscape. It serves as a reminder that securing digital assets is not just about building defenses but also about understanding the broader ecosystem of threats and actors. Companies may need to rethink their cybersecurity strategies, considering not only the threats posed by cybercriminals but also the potential interventions by unknown third parties.
For the cybersecurity industry, these events could spark a debate about the role of vigilante hackers in digital defense strategies. Should companies and law enforcement collaborate with such groups, or does that set a dangerous precedent? There’s also the risk that such interventions could inadvertently cause damage to systems or data, highlighting the need for clear ethical guidelines and accountability.
Investors should take note of this evolving landscape as it may influence the future direction of cybersecurity investments. Technologies and services that can adapt to these new dynamics or leverage the actions of vigilante hackers could present new opportunities. However, the volatile nature of these developments also suggests a need for caution and a deeper understanding of the risks involved.
As this story unfolds, the tech community will be watching closely to see if other hacker groups follow suit or if this phenomenon remains isolated. For now, the emergence of these digital vigilantes is a reminder of the ever-changing nature of cybersecurity threats and the innovative, albeit controversial, methods being employed to counter them. Founders and engineers should stay informed and flexible, ready to adapt their strategies to safeguard their digital assets in this unpredictable environment.