One command can now turn any open-source repository into an AI agent backdoor, thanks to a tool called CLI-Anything. This development, while innovative, raises serious security concerns that the tech industry cannot afford to ignore. OpenClaw has demonstrated that no current supply-chain scanner can detect these backdoors, posing a significant risk to software security.
Researchers at the University of Hong Kong’s Data Intelligence Lab recently introduced CLI-Anything, a tool that analyzes source code and generates a structured command line interface for AI coding agents. With support for Claude Code, Codex, OpenClaw, Cursor, and GitHub Copilot CLI, CLI-Anything has rapidly gained traction, amassing over 30,000 GitHub stars since its March launch. However, this same mechanism that integrates AI agents into software also opens the door to potential exploitation. The attack community is already discussing how to use CLI-Anything’s architecture offensively, highlighting a structural gap in current security measures.
The real issue lies not in what CLI-Anything does, but in what it represents. It creates SKILL.md files, which are instruction-layer artifacts that can be laced with malicious payloads. These poisoned skill definitions evade traditional security measures like CVEs and software bills of materials. As Cisco confirmed in April, traditional security tools were never designed to inspect the semantic layer where these instructions operate. This gap leaves the entire software supply chain vulnerable, and the attack community is well aware.
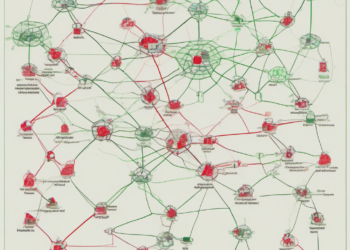
Traditional supply-chain security focuses on code and dependencies, but agent bridge tools like CLI-Anything operate on a separate, often invisible layer. This “agent integration layer” includes configuration files, skill definitions, and instruction sets that guide AI agents. While these elements don’t look like code, they execute like it, creating new vulnerabilities. Researchers have documented attack chains that exploit this layer, achieving bypass rates of up to 33.5% in some cases. The lack of a verification layer for these skill definitions means that AI agents can execute malicious instructions without detection.
The implications for the tech industry are profound. For security leaders, this is a wake-up call to audit their systems and inventory every agent bridge tool in use. Skills should be audited with the same scrutiny as package registries, and new scanning tools like Cisco’s Skill Scanner and Snyk’s mcp-scan should be deployed. Restricting agent execution privileges and instrumenting runtime observability are crucial steps to mitigate these risks.
For founders, engineers, and investors, the message is clear: the landscape is shifting rapidly, and the old models of security are no longer sufficient. The agent integration layer is a new frontier, and those who fail to adapt risk falling behind. The industry must act quickly to close this vulnerability window before it leads to widespread exploitation.
The next steps involve not just understanding the risks but actively taking measures to mitigate them. For developers, this means being vigilant about the tools and integrations they use. For investors, it’s about recognizing the companies that are proactive in addressing these emerging threats. As the tech world continues to evolve, the ability to adapt to these challenges will define the leaders of tomorrow.