Apple is doubling down on security with its latest enhancement to iCloud Keychain: escrow security. But does this new layer of protection truly address the concerns of its tech-savvy users, or is it just another feature wrapped in complex jargon?
## What Escrow Security Does
Apple’s escrow security for iCloud Keychain is designed to ensure that only authorized users can recover their data. This involves a multi-step authentication process, including verification via an iCloud account, password, and SMS confirmation. The heart of this system lies in clusters of hardware security modules (HSMs) that protect escrow records with encryption keys. If users successfully authenticate, the HSM cluster releases the escrow record, allowing the device to decrypt and restore the keychain.
The stringent security measures include a 10-attempt limit for authentication. Exceed this, and the HSM cluster will destroy the escrow record, rendering the keychain irretrievable. While this may sound like a nightmare scenario for users, it’s a robust defense against brute-force attacks.
## Market Landscape and Competitive Context
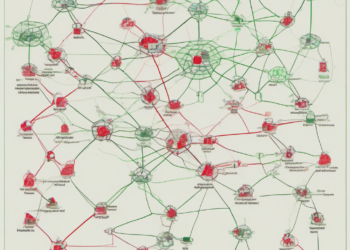
In a world where data breaches and cyber threats are rampant, companies are racing to bolster their security offerings. Apple’s move to enhance iCloud Keychain with escrow security isn’t isolated. Competitors like Google and Microsoft have also been ramping up their security protocols, emphasizing multi-factor authentication and encryption.
However, Apple’s approach is unique in its use of HSMs and the Secure Remote Password protocol, both of which add layers of security that competitors may not match. But the question remains: does this added complexity translate to tangible benefits for the end-user, or is it merely a technical flex?
## Implications for Founders, Engineers, and the Industry
For engineers and product managers, Apple’s escrow security introduces a new standard in data protection that could influence future product designs. The integration of HSMs and strict authentication limits might inspire similar innovations across the tech industry. However, it also raises concerns about user experience—specifically, the risk of data loss if users exceed the authentication attempt limit.
For founders and VCs, this development signals a growing market for advanced security solutions. As consumers become more aware of data privacy, startups focusing on cybersecurity could see increased interest and investment. Yet, the challenge remains to balance security with usability, ensuring that users aren’t alienated by overly complex systems.
## What Happens Next
Apple’s enhancement to iCloud Keychain is a clear nod to the increasing demand for data security. As the tech giant continues to refine its offerings, the industry will be watching closely to see if these measures set a new benchmark or simply add to the noise. For tech professionals, understanding these changes is crucial—not just for security, but for anticipating future trends in user data protection.